Today I will show you how we can enforce a Windows Information Protection (WIP) Policy on unmanaged devices using a Conditional Access (CA) policy. WIP is a Mobile Application Management solution for Windows 10 devices to keep your company data safe, even on personal devices.
In the past we could setup a WIP policy for devices which are unmanaged (not enrolled and managed by Intune) to keep our company data save, but we had no option to enforce this policy on unmanaged devices. Since a short while we have the option to create a Terms of Use as part of the Conditional Access and use that as a control in a CA policy. Because a Terms of use can only be accepted on a Azure AD joined or registered device, this allows us to force the WIP policy on personal devices.
Setup Windows Information Protection
To start using Windows Information Protection we first need to make sure Mobile Application Management (MAM) is enabled in Intune. WIP is the MAM version for Windows 10 devices.
- Open the Device Management portal and click Device enrollment – Windows Enrollment – Automatic Enrollment
- Make sure the MAM User scope is set to Some (and select a security group which contains your MAM users) or to All.
- Move to Client apps – App Protection Policies.
- Click Click Create policy
- Give you WIP policy a Name
- Choose Windows 10 as Platform
- Choose Without enrollment as Enrollment state
- Click the Protected apps tab
- Click Add apps
In this section we will add all the applications which are allowed to access our protected company data. There are two types of apps; enlightened and unenlightened apps. Enlightened apps are MAM (WIP) aware and unlightened apps are MAM unaware. Have a look it this Microsoft doc for more information.
- Select Recommended apps in the drop-down list
- Select all the required apps
- Click OK
- Click the Required settings tab
- Select the Windows Information Protection mode of choice (Read this doc for explanation of the different WIP modes).
- Enter you Corporate identity
- Click OK
In the next section we add the network boundaries. With network boundaries we determine where protected apps can access our corporate data. Have a look at this doc for the recommended network boundaries.
- Click the Advanced Settings tab and take a look at the notification about *AppCompat*.
It`s a good idea to add /*AppCompat*/ to the list of cloud resources. If you do not add this to your list of cloud resources, you`re not able to use third-part browsers like Chrome to access corporate data, as stated in the message. But even on personal device, like in my example WIP without enrollment, you should add it as you`re not able to use third-party browsers to browse the internet at all with out this added to the cloud resources. - Click SharePoint
The SharePoint boundary is 9 out of 10 times predefined. If it is not, use below as an example.
Go back to the advanced settings tab and click Add network boundary to add the other boundaries like below example of Outlook (Exchange Online).
The end result is a list of network boundaries.
Still on the Advanced settings tab most default settings are fine, but change them to your needs. Consider using a Data Recovery Agent (DRA) Certificate which allows recovery of encrypted data. This is highly recommend by Microsoft.
At the bottom of the advanced settings tab you will find Windows Hello for Business (WHfB) settings. By default WHfB is turned on. It allows you to turn off WHfB. When you leave it turned on it allows you to configure some settings like the minimum PIN length.
- When all settings are set, click OK and click Create.
- Click the Assignments tab
- Search the required security group with WIP users and select the group
- Click Save
Setup Terms of Use
The next step in our configuration is setting up our Terms of Use under Conditional Access. As written in the introduction, the Terms of use can only be accepted on devices which are Azure AD joined or registered. If we set this as a control as part of a Conditional Access policy, it forces our users to register their personal devices to gain access to company data. And we can enforce a Windows information Policy on those devices when the device is registered.
- Click Intune – Conditional Access – Terms of use
- Click New terms
- Give your Terms of use a Name
- Provide the Display name
- Upload a Terms of use document (PDF)
- Set Require users to expand the terms of use to ON (this is optional)
- Set Require to consent on every device to ON (This option is the most important requirement in this ToU setup, it forces your users to register their personal device)
- Under Conditional Access choose Create conditional access policy later
- Click Create
Setup Conditional Access policy
We need to setup a Conditional Access policy to set the Terms of use as requirement to allow access to corporate data.
- Click Intune – Conditional Access – New policy
- Give your CA Policy a Name
- Click the Users and groups tab
- Click All users to assign the policy to all users or click Select users and groups to assign it to a security group
- Click Done
- Click the Cloud apps tab
- Select All cloud apps
- Click Done
- Click the Conditions tab
- Click the Device platforms tab
- Click under Configure YES
- Click Select device platforms
- Mark Windows
- Click Done
- Click the Grant tab under Access controls
- Click Grant access
- Mark your Terms of Use
- Click Done
- Under Enable Policy click On
- Click Create
End-user experience
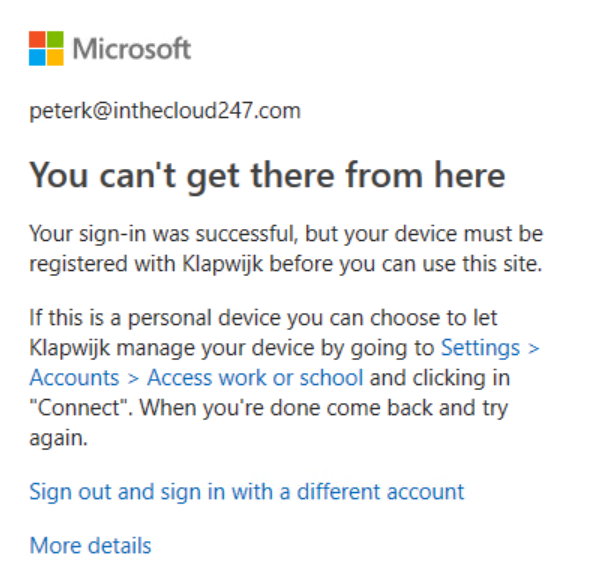
Everything is setup to protect our company data on personal devices. Let`s have a look at the end-user experience. On a personal (unmanaged) Windows 10 device open a browser and logon to the Office 365 portal. The user is presented a message like below with explanation why access to company data is prevented. The message also provides information on how to register the device.
When we follow the provided instructions, the users company account is added under Access work and school and the device is Azure AD registered. It looks almost the same as an Azure AD joined device, but if we click Info we can see the Management Server Address.
After clicking Info scroll down to Connection info to see the Management Server Address: wip.mam.management.microsoft.com. The Management Server Address when using Azure AD join/ Intune enrolled is r.manage.microsoft.com
After completing the device registration, open a browser and logon to the Office 365 portal. We are presented a screen with the Terms of Use which we need to accept. If the option Require users to expand the terms of use is set to ON, the user first needs to open the Terms before he is able to Accept the Terms.
When we now open, for example, SharePoint Online we see an icon of a briefcase in the right topcorner. When we hover over the briefcase with the mouse, a message shows the website is manage by the company.
SharePoint and OneDrive files are managed by Windows Information Protection when synced to the local device.
When we save a document with one of the applications of the Office ProPlus suite, it saves the document as a Work (WIP managed) document even if the location is not in de OneDrive synced folder. As an user, you still have the option to save a document as personal document, which is not managed by WIP (and is not removed during a wipe action).
Depending on the WIP Mode set, on the Required settings tab of the WIP policy, we have the option to change a Work document to a personal document.
Perform a App selective wipe
Let`s also have a look at a selective wipe request. When we perform a selective wipe, access to the documents which are managed by Windows Information Protection, is revoked. Personal documents can still be accessed after a wipe.
- Open the Device Management Portal
- Click Client apps – App selective wipe – Create wipe request
- Click the User tab
- Search for the user and select the user
- Click the Device tab
- All WIP managed devices are shown, select the device which need to be wiped
- Click create
Back at the Selective Wipe tab we can see the status of the wipe request. If the device is connected to the internet, the wipe is started soon after creating the request.
Back on the WIP managed device, when we try to open a Work document after the wipe request is complete, this will fail because access is revoked. Personal documents are untouched and can still be openen.
I hope this post is informative to you and reach out to me if you have any question.

Great Blog Peter! Thanks for sharing
Thanks Joost!
Great article! Unfortunally, i expirience one issue. With this condition applied, i can’t access o365 corporate resources by using Google Chrome. Did anyone had the same issue or it’s just me :)?
Hi Mario,
Please have a look at my note and the print screen about /*AppCompat*/
Without that added at the list of cloud resources you cannot use browsers like Chrome and Firefox to access your corporate data.
I added some additional info to that note to make clear you cannot access corp data without adding /*AppCompat*/ to the list of cloud resources.
Regards,
Peter
Hi Peter,
i added /*AppCompat*/ at the list of cloud Resources. Also added Windows 10 account extension into Chrome. When i turn off this CA policy, can access corp resource with Chrome. It’s definitly to policy, but i don’t see the connection.
But i also have some other unexpected behaivor from Chrome. Chrome is added as protected app to WIP policy, but works in personal context.
Ok, that sounds as the opposite as expected.
Must say I just (re)created the WIP policy in my lab and I`m not able to access any corp data with Chrome. I do some further testing.
Hi Peter,
i have an update. On monday thinks started to work as expected. Chrome works in enterprise context and is protected app. I noticed that some icons on Intune portal are changed, so maybe Microsoft pushed updates during weekend. Also, i changed Publisher for Chrome app. It was O=GOOGLE INC… to O=GOOGLE LLC, L=MOUNTAIN VIEW, S=CA, C=US. Even, i tried with Google LLC before, but it didn’t work.
BUT, i overlooked fact that you are talking about devices without enrollment. Expirence i described was with enrolled device.
On device without enrolmnet, still can’t access corp dana with Chrome.
But looks like, it is expected:
– Only enlightened apps can be managed without device Enrollment.
Iz
Hi Mario,
Good to read. Could you share with me where you found this info: Only enlightened apps can be managed without device Enrollment.
I`m able to allow Wordpad to access corporate data (only since today, in the weekend got an access denied). As far as I know that is not an enlightened app even it is an Microsoft app.
Hi Peter,
this is the link:
https://docs.microsoft.com/en-us/windows/security/information-protection/windows-information-protection/limitations-with-wip
This is also usefull link: https://docs.microsoft.com/en-us/windows/security/information-protection/windows-information-protection/create-wip-policy-using-intune-azure
That’s correct, wordpad isn’t listed as enlightened app.
Thnx for the info Mario, but indeed the documentation describes it “design to prevent personal files from being unintenionally encrypted by unenlighted apps. Unenlighted apps that need to access work using MAM need to be re-compiled as LOB apps or managed by using MDM with device enrollment.” And MS Support confirms.
Really useful info, Peter. We have a mixture of corporate desktop state:
1)AD joined
2)AD joined + AAD registered
3)AAD joined (MDM:Intune)
It will take us awhile to move all desktop to AAD joined. Am i right to say #1 and #2 will be considered as BYOD if we apply the method on this article?
Bryan,
Have not tested this with an AD joined device, but when the user tries to access Office 365 data the CA policy is applied and the Device is AAD Registered. So you end up in scenario 1 and 2 in a AD joined AAD registered device (like scenario 2). So you can consider it BYOD compared with my article 🙂
Hi Peter
I have the problem, when this Conditional Access Policy is active, I cannot enroll devices with autopilot. After autopilot detects my device correctly and sign in with my corporate credentials there comes the message “Your sign-in was successful but your device must be registered with…” and at this point I can not accept the Terms of use.. Is there something configured wrong?
Hi Adriano,
That`s a very good point. Used this in an environment where we didn`t use Autopilot.
But I assume when you exclude Microsoft Intune Enrollment in the CA policy as Cloud app, it should work.
Great blog, thank you.
When registering a device, the BYOD end user gets a prompt asking “Allow organization to manage this device”. If unticked, it will register with Azure AD and allow terms of use to be accepted, but the WIP policy will not apply.
If the box is left ticked, it will work as intended.
I wonder if there is a way to force the tick box “Allow organization to manage device”?
Many thanks