Azure Active Directory in the new Azure portal is in Preview now for a few months. Last week Microsoft announced Conditional Access in the new Azure portal at this article, which is situated in the portal under the Azure AD section. In this new blog I will explain in short what you could achieve with Conditional Access.
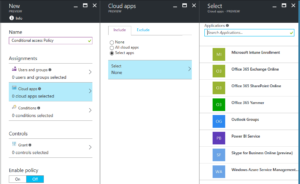 With Conditional Access you have the possibility to setup policies and restrict access to your corporate cloud applications, like Exchange and SharePoint Online. The policy consists of four parts; the user or group it is assigned to, the cloud apps which access to need to be restricted, the conditions and the controls.
With Conditional Access you have the possibility to setup policies and restrict access to your corporate cloud applications, like Exchange and SharePoint Online. The policy consists of four parts; the user or group it is assigned to, the cloud apps which access to need to be restricted, the conditions and the controls.
You must choose to what group the policy is assigned to and which apps are involved. That needs no further explanation.
The conditions (when should the policy be assigned) contains four settings. You can set a filter on sign-in risk; is it really the user who is signing in? There is a device platform filter; on which platform do you want to assign the policy? For example you can use this policy to restrict access to your apps for Windows devices only, so you can use MAM Policies for the mobile platforms. You can set a location filter; will this policy apply to all locations, or would you exclude your trusted IP? And the fourth condition, you have to ability to choose on which client app this policy is applied to. The browser, mobile apps and desktop clients or all these options.
After setting the conditions, you have the controls (what the action or requirement should be). At the controls you choose what will happen; block or allow access. When you choose to allow access, you have the options to require multi-factor authentication, require a compliant device (Intune compliant), to require a device to be domain joined or a combination of this requirements.
For example, with these conditional access policies it is possible to only allow access to Exchange Online from Windows devices which are domain joined. You have the control over the domain joined devices, so you now your data stays pretty save on these devices because of running anti virus software, enforcing group policies etc.

Does “domain joined” condition work for devices joined to AADDS (without on-perm AD)?
I have no luck with this setup and I’m not sure it is possible.
No, last time I checked this it needed to be on-prem AD joined.